Sometimes you need to run some command on remote computer. If you don’t want to bother user using Remote Assistance or user is not at the computer you can try Remote Powershell. Powershell was new feature when Windows Vista and Windows Server 2008 came. So we can divide operating systems into three categories. Each category requires some things and some requirements.
Windows 7 / Windows Server 2008 R2 and higher
Windows Vista / Windows Server 2008
- Needs everything from first group
- Needs to install PowerShell 2.0
Windows XP / Windows Server 2003
- Needs everything from second group
- Needs to install .NET Framework
Probably your environment will be mixed of all three types of operating systems. So let’s look how to configure it. I will use GPOs everywhere it can be used.
Enable Remote PowerShell for Windows Vista and Windows Server 2008
Create GPO and set following:
Computer Configuration > Policies > Administrative Templates > Windows Components > Windows Remote Management (WinRM) > WinRM Service > Allow automatic configuration of listeners (Allow Remote Server management through WinRM):

Firewall exceptions
Firewall exceptions for Windows 7 / Windows Server 2008 and higher
If you have Microsoft firewall closed and you need to make exception using GPO in Computer Configuration > Policies > Administrative Templates > Network > Network Connections > Windows Firewall > Domain Profile > Windows Firewall: Define inbound port exceptions:

Firewall exceptions for Windows XP / Windows Server 2003
You have to define New Firewall rule under Computer Configuration > Policies > Windows Settings > Security Settings > Windows Firewall with Advanced Security > Windows Firewall with Advanced Security > Inbound Rules and create new Inbound rule with predefined type “Windows Remote Management”:

Configure Service
To enable Remote Powershell I need to configure service. WinRM service has to start automatically. Create new setting in GPO in Computer Configuration > Policies > Windows Settings > Security Settings > System Services. Setup service Windows Remote Management (WS-Management) following way:

Let’s change startup for this service using GPO settings under Computer Configuration > Preferences > Control Panel Settings > Services. Create new Service setting with following settings:


Windows XP / Windows 2003 specialities
To make Powershell work remotely on older operating systems you need to make sure your operating systems have installed two hotfixes: KB968930 and KB951847. These hotfixes are distibuted via Windows Updates so if you use WSUS, there updates are already on your older operating systems.
To enable PowerShell for remote connection you need to enable it using startup script. So you need to create new GPO which will run only on older OS. You can use following WMI filter to make this GPO apply only on older OS:

You can use following script as a startup script to enable Powershell Remote for Windows XP.
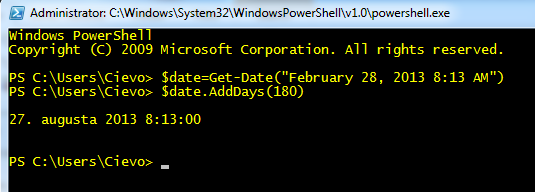
To test it you can run following command:
Enter-PSSession -ComputerName COMPUTER_NAME
Active Directory Users and Computes Implementation
To make it look better you can implement connection to computer using Active Directory Users and Computers.
On location \\domain.local\NETLOGON create new Powershell.vbs file:
' ' Script to run Remote Powershell on domain computer '
Set wshArguments = WScript.Arguments Set objComputer = GetObject(wshArguments(0))
' ' Check if Remote Assistance is installed '
Set fso = CreateObject("Scripting.FileSystemObject")
If (fso.FileExists("C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe")) Then
' Is istalled
Set objShell = WScript.CreateObject("WScript.Shell")
Return = objShell.Run("C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe -noexit \\domain.local\NETLOGON\Remote_Session.ps1" & objComputer.dNsHostName, 1, false)
Else
' Is not installed, error.
Wscript.Echo "Microsoft Remote PowerShell is not enabled on this machine."
End If
On location \\domain.local\NETLOGON create new Remote_Session.ps1 file:
[CmdletBinding()]
Param(
[Parameter(Mandatory=$True,Position=1)]
[string]$computerName
)
Enter-PSSession -ComputerName $computername
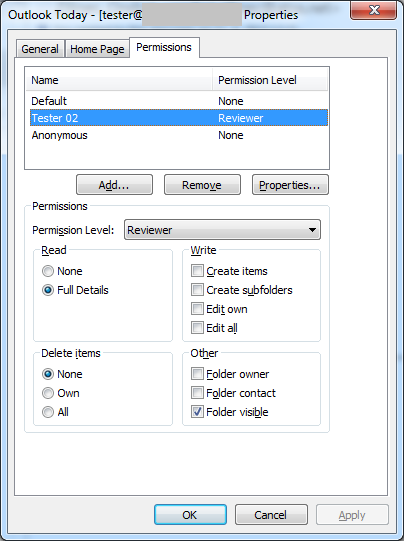
When files are ready, you need to create new record in Active Directory using adsiedit.msc. Connecto to configuration partition of your domain:

Go to Configuration > CN=Configuration,DC… > CN=DisplaySpecifiers > CN=409 > CN=computer-Display and edit property called adminContextMenu.
Add another record into existing list of records. I used following record:
3, &PowerShell Remote,\\domain.local\NETLOGON\Powershell.vbs
which means:
3 – order of record in the list of records (if you have only one existing record, your number will be 2)
&PowerShell Remote – name of the item in context menu
\\domain.local\NETLOGON\Powershell.vbs – path to vbs script you created
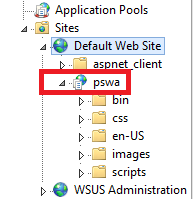
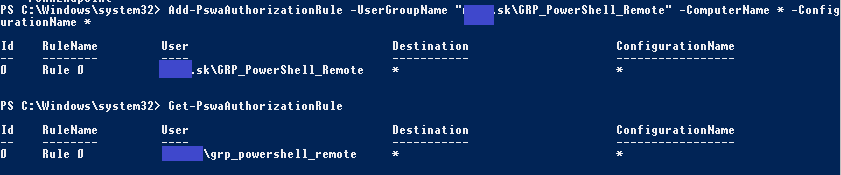
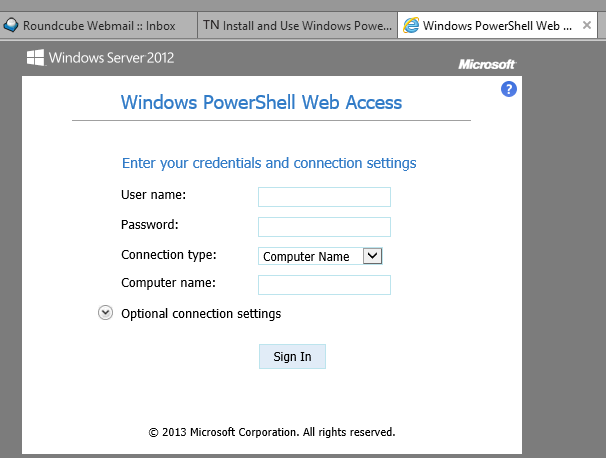
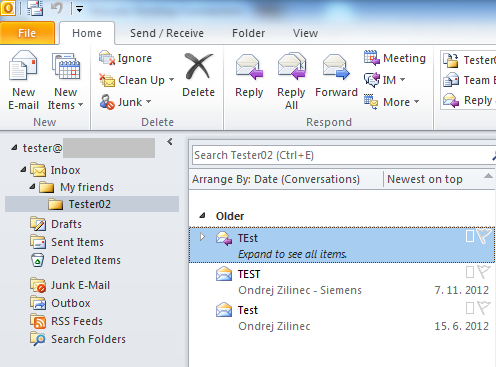
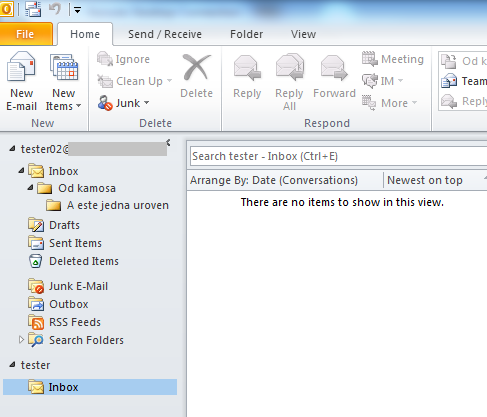
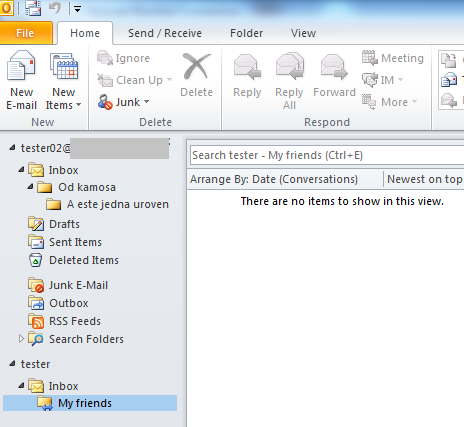
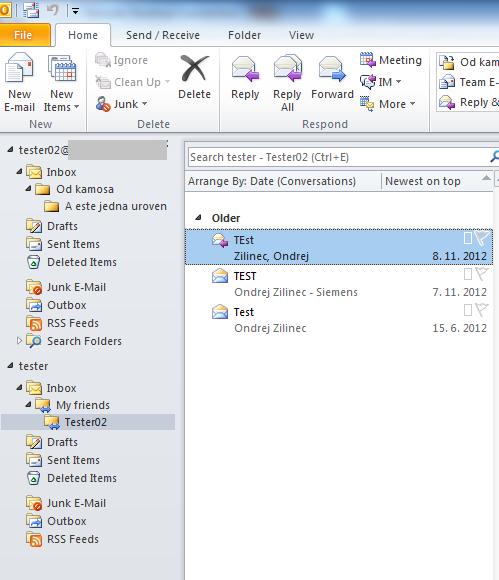
Here is how it looks in one of the environments:

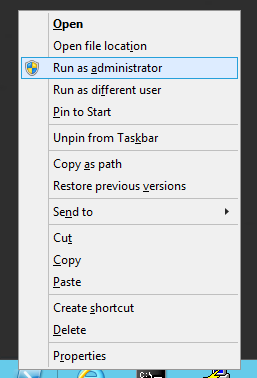
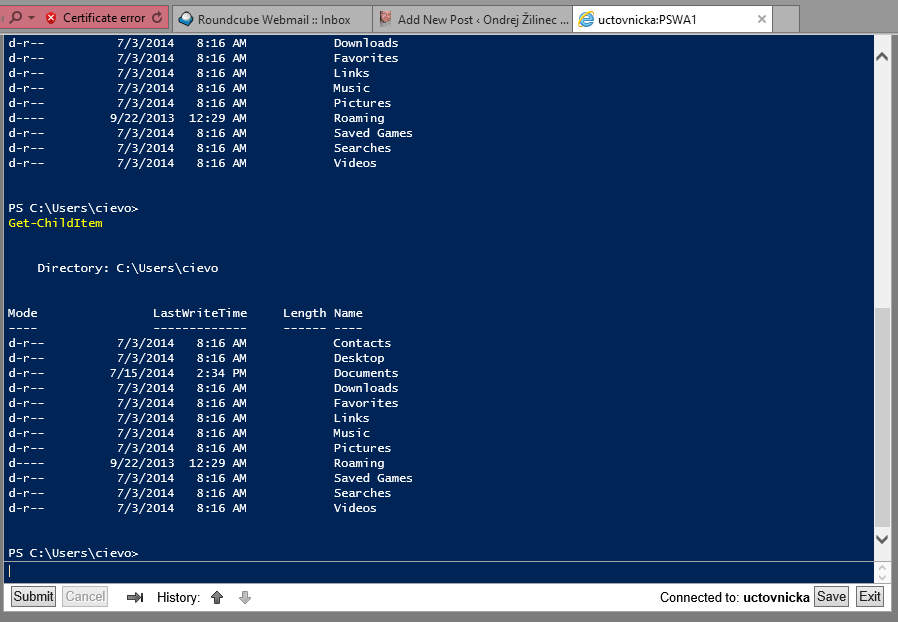
When all is done, your Active Directory Users and Computers console has to be reopened and you will find new record under computer account:

When you click on this new item in context menu new powershell window opens. This powershell window is remote powershell windows from remote computer.
I hope people start using powershell more often,
Recent Comments